Use cases
Where secure data intelligence earns its keep.
Discover how Checkall Analytics engages in real-world scenarios and how our custody-grade discipline changes the outcome.
- UC/01 · Secure Cloud + Evidence Storage
National prosecutor's office: custody vault for a multi-year corruption case
Explore service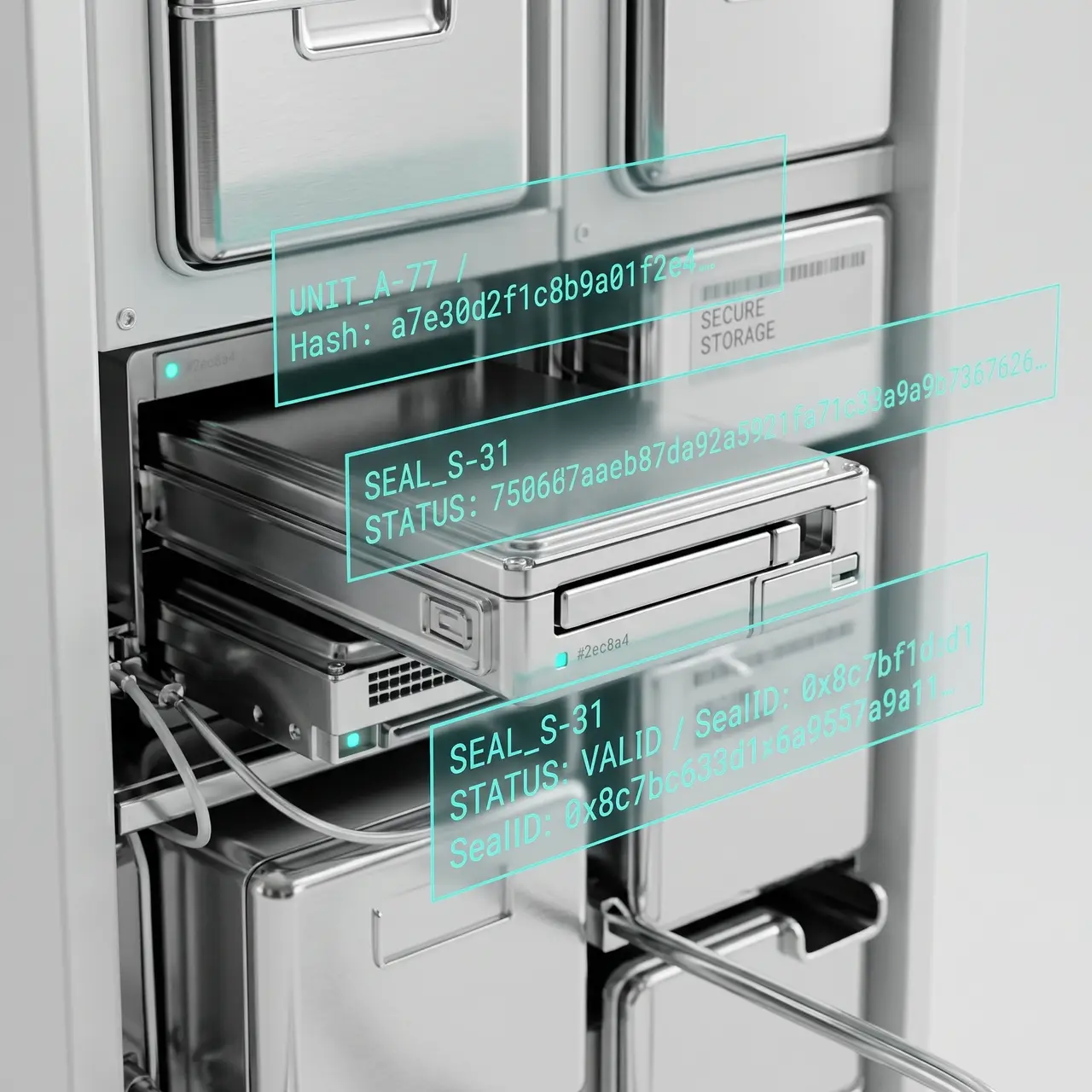
A prosecuting authority running a complex, multi-year matter needed a single, defensible home for evidentiary data spanning seized devices, intercepted communications, financial records, and witness materials. Off-the-shelf storage could not produce a chain of custody that would survive challenge.
What the client needed
- Immutable storage with full chain of custody
- Controlled hand-off packages for trial bundles
- Access governance across multiple investigative teams
- Auditable retention through appeal cycles
Outcome
A custody-grade vault with cryptographic integrity, granular access logging, and repeatable hand-off — designed to outlast the case and survive cross-examination of the process itself.
- UC/02 · Advanced AI & Machine Learning
Tier-1 bank: anomaly detection cuts fraud-investigation cycle time
Explore service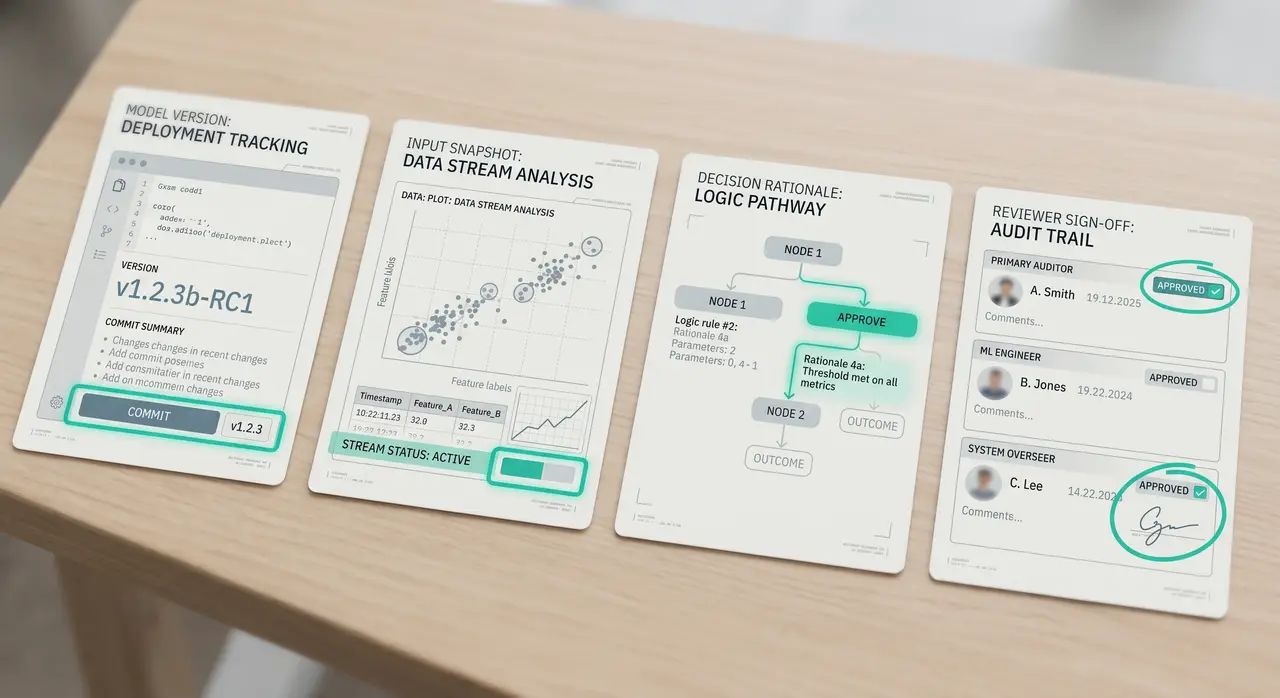
A retail bank fraud team was losing time triaging alerts that lacked context. Investigators needed signals ranked by likelihood and explained — not just flagged — and the bank needed every decision to be auditable.
What the client needed
- Anomaly detection across transactional and behavioural data
- Explainable rankings investigators could defend
- Audit trails for every model output
- A pipeline that fit inside existing risk governance
Outcome
A measurable reduction in cycle time per investigation, fewer false positives reaching investigators, and a model-governance trail that satisfied internal audit and the regulator.
- UC/03 · Digital Forensics
Listed corporate: mobile + cloud forensics in an executive misconduct probe
Explore service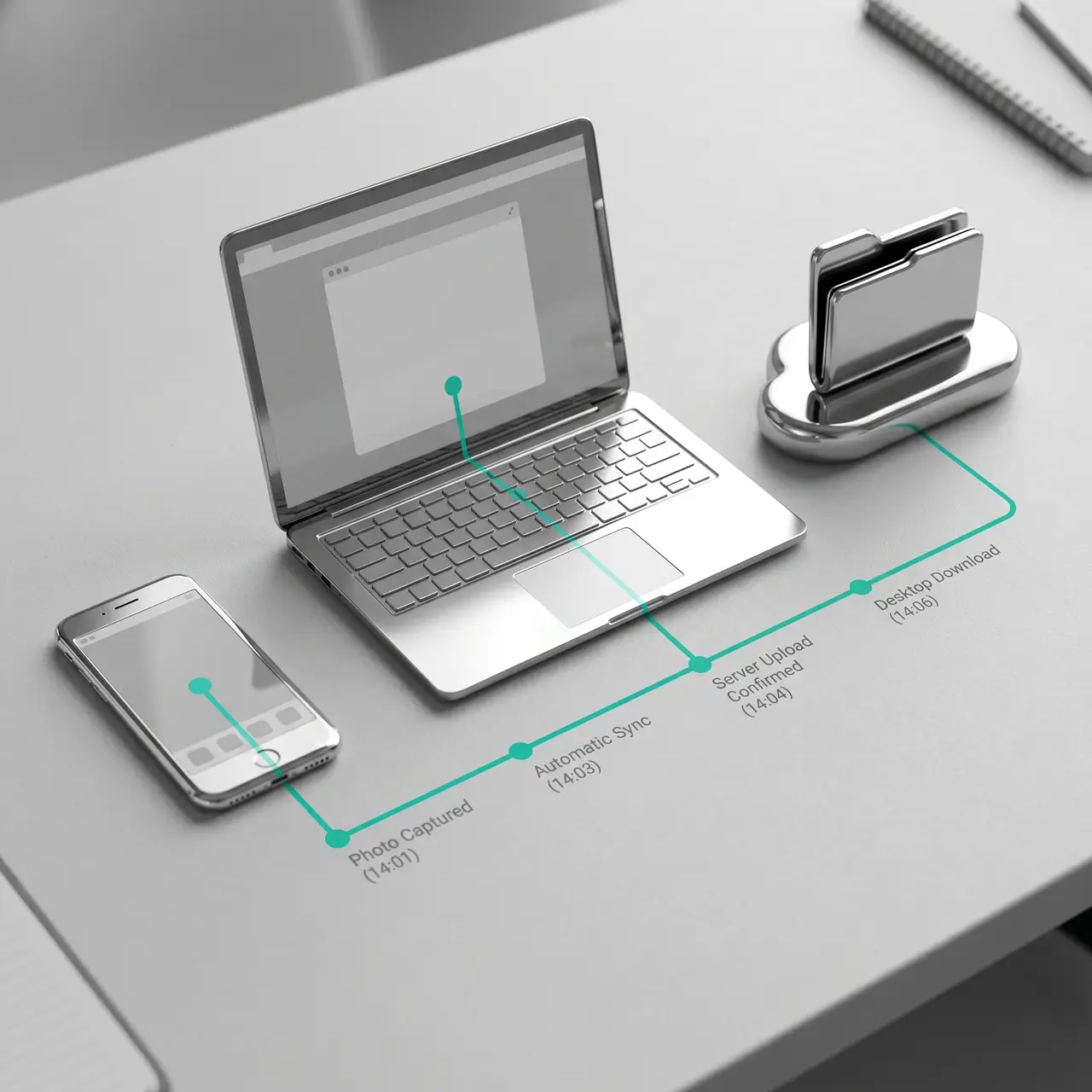
An audit committee commissioned an independent inquiry into senior-leadership conduct. Relevant artefacts spanned company-issued and personal devices, several cloud accounts, and a sensitive communications platform. The committee needed defensibility — and tact.
What the client needed
- Defensible acquisition across mobile and cloud sources
- Reconstruction of communication and document timelines
- Reporting that worked for legal counsel and the board
- Custody preserved through any subsequent regulatory referral
Outcome
A documented forensic record with an evidentiary trail intact, a clear timeline of relevant events, and a report the committee could act on — discreetly, and with the option to escalate.
- UC/04 · Cybersecurity
Healthcare provider: breach response and POPIA-grade posture rebuild
Explore service
A healthcare provider experiencing an active breach needed containment and investigation in parallel — without losing the evidentiary trail required by POPIA notification and downstream civil exposure. Existing security tooling was fragmented across vendors.
What the client needed
- Immediate containment and incident response
- Forensic preservation of attacker activity
- POPIA-aligned breach notification support
- A path back to a coherent, defensible security posture
Outcome
Containment within the response window, a forensic record sufficient for regulatory engagement, a notification process that held up under scrutiny, and a 12-month posture-rebuild programme — including SOC, vCISO, and ISO 27001 alignment.
Facing a similar situation?
Discuss your requirement in confidence.
If your situation looks like one of these — or sits in the seams between them — outline it through the contact form. We respond in confidence.