Cybersecurity
Advisory and operational depth, on one team.
Security is not a programme bought once. We work with clients across the full arc — strategy, architecture, operations, and incident — with the same team that handles the forensic and evidentiary aftermath when something does go wrong.
Designed for work that has to hold up under pressure.
Advisory and operational — vCISO, managed SOC, penetration testing, incident-response retainers, and compliance for POPIA, ISO 27001, and SOC 2.
- CISOs and security leaders
- IT leadership at growing organisations
- Risk and compliance owners
- Boards and executives wanting credible assurance
What is in scope.
- 01 Virtual CISO (vCISO) advisory
- 02 Managed Security Operations Centre (SOC)
- 03 Penetration testing and red-team exercises
- 04 Incident-response retainers
- 05 POPIA, ISO 27001, and SOC 2 compliance programmes
- 06 Security architecture review and roadmap
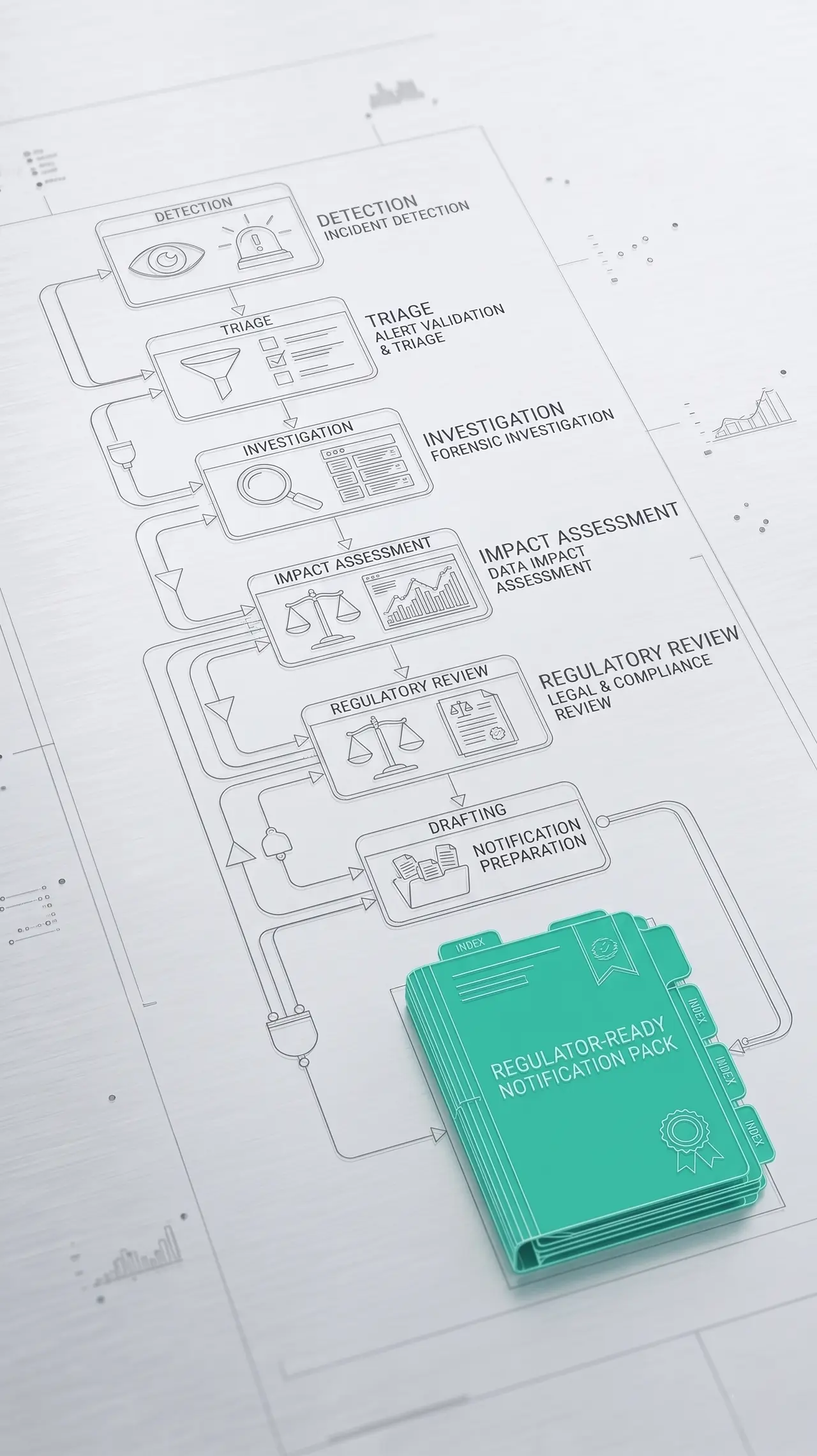
Engagement flow
How the work is usually structured.
The sequence flexes with the matter, but the operating logic stays consistent from first scope to final hand-off.
- 01
Advisory plus operations
A vCISO without operational reach is theory. A SOC without strategy is noise. We bring both, and the people doing the strategy speak the same language as the people on the keyboard at 2am.
- 02
Compliance that actually reduces risk
POPIA, ISO 27001, and SOC 2 programmes are built to deliver real control improvements — not paperwork. The certificate is the by-product of a posture you can defend.
- 03
When prevention fails
Our incident-response retainers connect directly to our forensic and evidence-storage practices. Containment, investigation, and custody happen inside one chain — not handed across vendors.
What you should expect to leave with.
Not more activity. Clearer custody, cleaner decisions, and outputs that survive scrutiny.
- 01
A security posture you can describe to a board
- 02
24/7 detection and response without commodity drift
- 03
Compliance certifications that reflect real controls
- 04
Faster, cleaner incident handling — with custody preserved
Adjacent services
Most engagements span more than one service.
Start a conversation
Ready to scope a Cybersecurity engagement?
Outline the situation. We will scope the right combination of pillars, custody, and team — and respond in confidence.